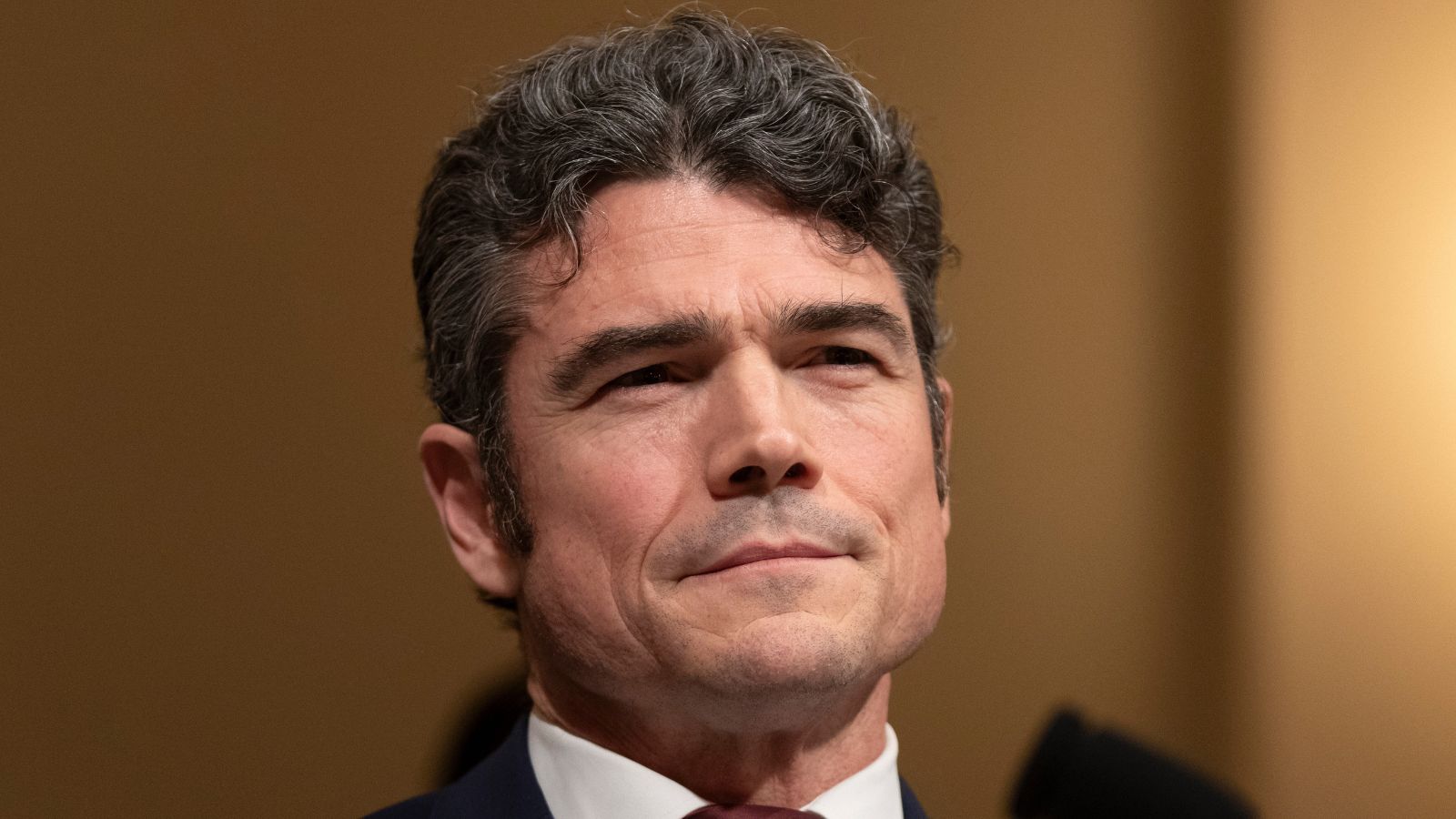
The appointment of Joseph Kent as a top U.S. counterterrorism official represents a transition from theoretical policy-making to high-stakes operational realism. While most biographical accounts focus on the tragic narrative of his first wife, Shannon Kent, who was killed in a 2019 ISIS suicide bombing in Manbij, Syria, a rigorous analysis must look beyond the personal loss to examine the structural shift in American intelligence. Kent’s profile is not merely a human-interest story; it is a case study in the integration of specialized tactical experience into the highest levels of the National Security Council (NSC). This integration addresses a historical bottleneck in Washington: the disconnect between "White House" strategy and "ground-truth" execution.
The Manbij Inflection Point and Tactical Intelligence Failures
The January 16, 2019, bombing in Manbij was not an isolated act of terror but a failure of specific intelligence parameters. Shannon Kent, a Chief Cryptologic Technician, was part of a specialized cell designed to provide real-time signals intelligence (SIGINT) to ground forces. Her death, alongside three other Americans, exposed the fragility of the "small footprint" model in active conflict zones. Also making waves in this space: The Kinetic Deficit Dynamics of Pakistan Afghanistan Cross Border Conflict.
The event catalyzed a shift in how the U.S. evaluates the risk-to-reward ratio of deploying high-value intelligence assets in semi-permissive environments. Joseph Kent’s subsequent trajectory from a career in the Special Forces (Green Berets) and the Central Intelligence Agency (CIA) to a policy-making role at the NSC signifies a departmental effort to close the "feedback loop" between technical collectors and strategic planners.
The Three Pillars of the Kent Strategic Framework
To understand Kent's influence, one must categorize his operational philosophy into three distinct pillars: More information into this topic are covered by Associated Press.
- Direct Action Realism: A departure from the "forever war" paradigm, favoring targeted, objective-based strikes over prolonged nation-building. This approach treats counterterrorism as a maintenance function rather than a solvable problem.
- Intelligence Front-Loading: Prioritizing the safety and utility of human and technical assets by integrating their feedback directly into the mission-planning phase, rather than treating them as secondary support.
- Bureaucratic Agility: Utilizing his experience in both the military and the intelligence community (IC) to bypass the traditional silos that often delay response times during active threats.
Quantifying the Cost of Information Asymmetry
In counterterrorism, information asymmetry occurs when the adversary possesses localized knowledge that the state cannot replicate through satellite or electronic means. Shannon Kent’s role was to bridge this gap. Her loss quantified the "cost function" of human intelligence (HUMINT) in the Levant.
When Joseph Kent entered the political and policy sphere, he brought a specialized understanding of this cost function. He argues that the U.S. has historically over-indexed on broad geopolitical goals while under-valuing the specific tactical risks posed to elite specialists. This creates a friction point within the NSC: the tension between the desire for a total "pivot" away from the Middle East and the reality of persistent, low-level insurgencies that require constant monitoring.
The Evolution of the Special Operations Liaison
Kent’s rise illustrates the increasing "special-operatization" of U.S. foreign policy. Traditionally, the NSC was populated by academics and career diplomats. The inclusion of an individual with Kent’s specific background—Special Forces combat experience combined with CIA operational expertise—shifts the internal logic of the council toward a "kinetic-first" perspective on threat mitigation.
Operational Variables in Modern Counterterrorism
The effectiveness of Kent’s leadership can be measured through several key variables that define the current threat environment:
- Attribution Speed: The time elapsed between a kinetic event and the positive identification of the perpetrator. Kent’s focus remains on shortening this window through integrated SIGINT/HUMINT pipelines.
- Resource Allocation Efficiency: The ratio of specialized personnel to general support staff. Kent advocates for leaner, more autonomous units that can operate with minimal logistical tails.
- Deterrence Credibility: The psychological impact of U.S. strikes on non-state actors. The strategy here is not just to eliminate targets but to demonstrate a persistent, "over-the-horizon" capability that renders traditional sanctuary useless.
The Structural Conflict of the "America First" Doctrine
Kent’s alignment with "America First" foreign policy introduces a paradox in counterterrorism. On one hand, the doctrine calls for a reduction in foreign entanglements; on the other, Kent’s personal and professional history is defined by the necessity of deep involvement in those very regions to prevent domestic attacks.
This creates a bottleneck in policy execution. To resolve this, Kent’s strategy utilizes a "hub-and-spoke" model of regional security. The U.S. acts as the technical "hub," providing intelligence, air support, and high-level coordination, while local "spokes" (partner forces) handle the bulk of the physical territory holding. This limits American exposure—the primary variable in the political cost of war—while maintaining an active kill chain against high-value targets.
Mechanical Analysis of the Manbij Incident
To understand why Kent’s perspective is considered "high-authority," one must deconstruct the mechanics of the attack that killed his wife. The suicide vest used in Manbij was a low-tech solution to a high-tech presence. It bypassed the electronic warfare suites and encrypted communications of the U.S. team by utilizing the "crowd camouflage" of a civilian restaurant.
This specific failure mode—the inability of sophisticated technology to counter primitive, decentralized aggression—is the cornerstone of Kent’s skepticism toward "sanitized" warfare. He operates under the assumption that there is no technological silver bullet for counterterrorism; instead, there is only the constant, iterative process of risk management and the "mowing the grass" philosophy of periodic disruption.
The Intelligence Community’s Cultural Pivot
Kent represents a broader cultural shift within the IC. For decades, the divide between the "analysts" (who write the papers) and the "operators" (who pull the triggers) was nearly impenetrable. Kent’s career spans both worlds. This dual-track expertise allows him to challenge the underlying assumptions of intelligence reports that may lack tactical context.
The "Kent Effect" in the NSC likely manifests as a rigorous vetting of intelligence products. When a report suggests a "low risk" for a specific deployment, Kent’s presence ensures that "low risk" is defined by the actual conditions on the ground—vulnerabilities in transit, local informant reliability, and medical evacuation windows—rather than just geopolitical sentiment.
Critical Limitations of the Operationalist Approach
Despite the benefits of having a practitioner at the helm, the operationalist approach has inherent limitations:
- Tactical Over-Fixation: Focusing so intently on the "how" of a mission that the "why" becomes obscured. Eliminating a cell may be tactically successful but strategically neutral if it does not alter the underlying radicalization cycle.
- Confirmation Bias: An operator-turned-policymaker may over-rely on kinetic solutions because those are the tools they have mastered, potentially overlooking diplomatic or economic levers that could provide more sustainable stability.
- Survivor Bias: Kent’s success in surviving a career in special operations may lead to a higher tolerance for risk in others, assuming that elite training can always overcome systemic failures.
Assessing the 2026 Threat Landscape
As of March 2026, the global counterterrorism landscape has moved away from large-scale territorial caliphates toward "digital-first" radicalization and decentralized cells. This transition renders the 2019 Manbij model somewhat archaic, yet Kent’s emphasis on SIGINT remains relevant. The new battlefield is defined by encrypted messaging apps and cryptocurrency-funded logistics.
Kent’s role involves overseeing the modernization of the U.S. "hunt" capability. This includes:
- AI-Driven Pattern Recognition: Using machine learning to sift through massive datasets of intercepted communications to identify anomalies that precede an attack.
- Financial Interdiction: Leveraging the transparency of blockchain technology to track the movement of funds from state sponsors to proxy groups.
- Cyber-Kinetic Integration: Coordinating cyberattacks on insurgent infrastructure simultaneously with physical raids to maximize confusion and disruption.
The Personal/Professional Dichotomy
The narrative of Joseph Kent is often framed as a quest for closure. However, in the realm of national security strategy, personal loss is a data point—a brutal lesson in the failure of specific defense protocols. Kent’s value to the NSC is not his status as a "Gold Star" spouse, but his ability to translate that loss into a rigorous interrogation of current security posture.
He identifies the "unforced errors" in policy that lead to casualties. For example, the decision to maintain a predictable presence in Manbij despite known insurgent activity in the surrounding areas. By viewing the world through the lens of tactical vulnerability, Kent forces the administration to confront the reality that every policy choice has a physical consequence for those tasked with its enforcement.
Strategic Recommendation for Counterterrorism Policy
The U.S. must formalize the "Kent Doctrine" by creating a permanent "Ground Truth Liaison" within the NSC. This role should be exclusively filled by individuals with at least a decade of combined tactical and intelligence experience. This formalizes the bridge between the boardroom and the battlefield, ensuring that strategic goals are never divorced from the mechanical realities of their execution.
Furthermore, the IC must pivot its recruitment and training to reflect this hybrid model. The traditional separation of analyst and operator is a liability in an era of rapid-cycle conflict. Future leaders must be capable of deconstructing a geopolitical crisis in the morning and auditing a tactical mission plan in the afternoon. This requires a curriculum that emphasizes both macroeconomic theory and the physics of modern weaponry.
The final strategic play is to accept that counterterrorism is a game of attrition, not a war of annihilation. The goal is to drive the "cost of aggression" for the adversary so high that it becomes unsustainable, while simultaneously lowering the "cost of intervention" for the state through technical innovation and specialized, high-impact leadership.